DORA, NIS2, and the SEC's cybersecurity disclosure rules have made third-party risk a board-level accountability.
The threat landscape is compounding the pressure: software supply chain compromises, AI tool proliferation, and concentration risk across technology providers and supplier ecosystems are routine exposures now, not edge cases. What’s changing is how organizations are responding. The programs gaining ground are integrating TPRM into the broader risk and compliance function, using vendor intelligence to shape executive decision-making and enterprise risk posture rather than routing it through an annual review cycle.
What follows covers the full scope: what TPRM is and what’s driving its adoption, how a mature program is structured across the vendor lifecycle, the measurable benefits of getting it right, and the implementation traps that consistently set programs back, whether you’re standing up a program for the first time or pressure-testing an existing one.
What is Third-Party Risk Management?
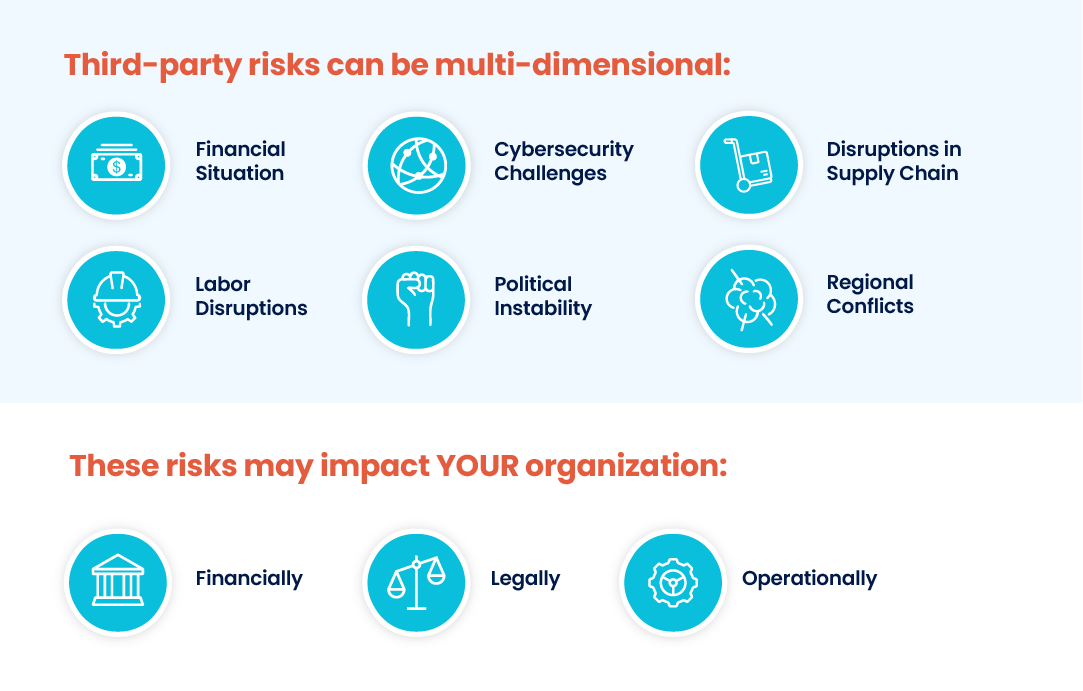
第三方风险管理(TPRM)是一个识别、评估和降低与外部第三方(如销售商、供应商、承包商和业务合作伙伴)合作相关风险的过程。它涉及彻底的尽职调查,以应对可能影响组织运营、财务健康、网络安全、法律地位或服务客户能力的潜在风险。这些风险可能包括网络安全事件、供应链中断、劳动力短缺、金融不稳定、政治因素和地区冲突。TPRM 使组织能够主动管理风险并制定应对计划,而不是在问题出现时才做出反应,从而确保业务连续性并保护关键利益相关者。
The Third-Party Risk Management Lifecycle: Process Stages and Workflow
The value of TPRM begins with the process of identifying risks and extends throughout the entire lifecycle of the relationships between your organization and your vendors. From initial vendor selection to final offboarding, each stage in your workflow requires thoughtful oversight.
The TPRM lifecycle includes:
-
Sourcing and Selection: This phase includes evaluating each potential vendor’s ability to meet service or solution requirements and scoring baseline security, privacy, reputational, and financial risks. This can be accomplished by conducting questionnaire-based assessments, accessing vendor intelligence databases, or a combination of both.
-
Intake and Onboarding: Once vendors are selected, they are onboarded into a central repository via manual or bulk upload. This can be accomplished through intake forms completed by internal stakeholders, spreadsheet imports, or an API to an existing vendor management or procurement solution.
-
Inherent Risk Scoring: Inherent risk is a vendor’s risk level before accounting for any specific controls your organization requires. It is best practice to score a vendor’s inherent risk with a simple assessment before giving them access to your systems and data. This also enables you to determine the required level of due diligence and the frequency and scope of subsequent risk assessments.
-
Internal Controls Assessment: Controls assessments can be used during initial due diligence and periodically to satisfy audit requirements. Risks identified during the assessment process are usually scored according to impact, likelihood, and other factors. Results can also be mapped to key requirements in other compliance and security frameworks, such as ISO, NIST, or SOC 2.
-
External Risk Monitoring: By tapping into external sources of continuous third-party intelligence, you can cover gaps between periodic assessments and validate assessment responses against external observations. Risk monitoring can include cyber intelligence, business updates, financial reports, media screening, global sanctions lists, state-owner enterprise screening, politically exposed person(PEP) screening, breach event notifications, and more.
-
SLA and Performance Management: Assessments and monitoring can be used to determine whether vendors are meeting their obligations throughout the business relationship. For instance, this can include evaluating their ability to deliver against SLAs, apply remediations, or meet compliance requirements.
-
Offboarding and Termination: During this phase, assessments ensure that all final obligations have been met. This can include contract reviews, settling outstanding invoices, removing access to systems and data, revoking building access, and reviewing privacy and security compliance.
When planning your TPRM approach, remember that the parties’ circumstances may change at any point during the engagement. Detecting and managing those changes is critical to your organization’s success. Vendors may change business operations, their supply chain for key materials may be disrupted, or regional bodies may change import/export requirements. For example, data privacy laws are changing rapidly around the world. All of these conditions are happening today, and the companies that have effectively implemented a TPRM process are thriving while others are falling behind.
Given the rapid pace of change, there is a corollary need for organizations to monitor and perform initial analysis of available information in near real time to identify and manage their risk. This requirement mandates that some of the processes automate the collection and dissemination of information about third-party vendors. Effective automation enables your TPRM office to identify risks and drive remediation before your organization suffers reputational risks.
第三方风险管理计划驱动因素
Several regulatory and compliance requirements mandate the management of 3rd party risk and can provide an effective framework for mitigating vendor risk. Regulatory requirements that drive TPRM programs cover a broad spectrum of markets, vendors, and data, and are often driven by the type of organization (e.g., regulations and guidelines from CMMC, EBA, FCA, FFIEC, HIPAA, NERC, NIST, NYDFS, OCC, and others), the location of your organization (e.g., privacy, state charter requirements), or your customers’ location (e.g., GDPR, CCPA). The key point to understand regarding these requirements is to ensure that your program accounts for which data your organization is liable to protect, where your customers typically reside, and the standard requirements your vendors must meet to deliver their services. Include these requirements in your agreements and extend them to vendors working with the covered data.
Implementation of TPRM programs by organizations is driven by the following:
- 遵守监管要求。
- 网络安全风险。
- 有效的 TPRM 计划的竞争优势。
- 内部采购/效率驱动因素。
- 管理内部财务和业务风险。
- 满足客户要求。
无论贵组织建立 TPRM 计划的具体驱动力是什么,在建立工作流程的过程中,确定并与所有内部利益相关者(如高管、董事会、采购、内部审计、财务、IT、信息安全、法律和合规)合作至关重要。
谁应该参与第三方风险管理?
When implementing a TPRM program, ensure that all impacted internal and external stakeholders are included in establishing it. At a minimum, consider the following as internal stakeholders:
- 高管(首席执行官、首席财务官、首席信息官、首席运营官、首席信息安全官等)
- 总顾问
- 董事会成员
- 内部审计员
External stakeholders are another critical constituency to consider in the development of your program. External stakeholders include:
- 供应商
- 监管机构
- 客户

Since TPRM programs seldom start at a company’s inception, it is important to consider the existing agreements/programs in force with external vendors and ensure they are thoroughly analyzed against the proposed TPRM program. Ensure that discrepancies are recorded and that a plan to address unmitigated risks is created and tracked to completion.
监管 TPRM 风险管理的影响因素
监管标准是 TPRM 计划的主要驱动力。监管计划具体针对
- 医疗保健
- 联邦政府合同
- 接受信用卡
- 金融服务
- 银行业
- 制造业

All of these require implementing a full-lifecycle process for TPRM. These requirements are typically driven by the type of sensitive data collected in the standard course of business.
A primary example of this kind of regulatory-driven risk management is an important part of the industry-standard PCI-DSS, which defines third-party providers and requires that providers not transmit cardholders “data on behalf of customers or organizations to providers that may compromise the security of their data and environment.” This means that while companies are obliged to develop the required cybersecurity program for themselves, they are still required to monitor vendors’ cybersecurity programs that handle access to sensitive data, even if those vendors keep the risk below a certain threshold.
Another example is federal programs and contracting that require strict security management of all vendors with access to the information. This process goes far beyond simple questionnaires and the exchange of documentation; it may also include scanning internal environments and legal representations from executives regarding the data protection in place. The complexity of the third parties involved, the potential for conflicts of interest, and the risk of financial losses are driving companies to continuously improve their risk management practices and risk mitigation strategies.
The traditional TPRM model relied on on-site visits, manual questionnaire review, and consultant-led assessments conducted at defined intervals. That approach cannot keep pace with the scale and distribution of modern vendor networks. Organizations managing hundreds or thousands of third parties across multiple geographies require automated data collection, continuous monitoring, and workflow tooling to assess and track vendor risk at the speed the environment demands.
Coupling current conditions with the rapidly increasing risk complexity and reach of supply chains today, this simply isn’t feasible using traditionally successful processes. Success at TPRM requires greater use of automation and tools designed to collect and perform initial analysis of vendor data.
人工智能在 TPRM 中的作用
随着企业越来越依赖相互关联的供应链和第三方关系,全面的风险洞察和及时的决策势在必行。来自不同来源的数据呈指数级增长,为利用 人工智能和高级分析提供了机会,从而实现更深入的风险评估、预测能力和实时监控。监管审查的增加和复杂威胁的激增,进一步要求采用数据驱动和人工智能驱动的方法进行风险管理。
Adopting artificial intelligence (AI)-related technologies can be instrumental in strengthening a modern TPRM program. AI’s capabilities streamline TPRM and supplier risk management (SRM) processes, providing a more efficient and proactive approach across complex third-party networks:
- 任务自动化: 人工智能驱动的系统可以简化日常的第三方风险评估、数据分析和报告。这可以提高效率和准确性,同时帮助第三方风险经理专注于更高层次的活动。
- 预测分析: 人工智能模型可以分析历史数据和模式,预测潜在风险,帮助您采取积极措施降低风险。
- 异常检测:人工智能算法可以识别可能预示着欺诈、安全漏洞或其他风险的异常模式或行为。
TPRM 的价值何在?
A third-party risk management program delivers value across the entire vendor lifecycle, from initial selection through offboarding. Here is what a mature program gives your organization:
-
Third-Party Visibility
TPRM provides a structured, centralized view of which vendors have access to your systems and data, the services they provide, and the risks they pose. Without this visibility, organizations cannot accurately assess their exposure to disruptions caused by third- and fourth-party networks.
-
Early Risk Detection
Combining periodic assessments with continuous monitoring enables your organization to identify risks before they become incidents. Organizations that detect issues early spend less time in crisis response and more time on deliberate risk decisions.
-
监管合规
Most major compliance frameworks — including HIPAA, PCI DSS, GDPR, and CMMC — require documented evidence of third-party risk controls. A structured TPRM program produces the assessment records, audit trails, and remediation documentation that regulators and auditors expect.
-
Reputational Protection
Third-party incidents carry reputational consequences that extend well beyond the vendor relationship itself. Organizations with mature TPRM programs are significantly less likely to suffer brand damage following a publicized breach or vendor-related compliance failure.
-
竞争优势
Organizations that can demonstrate a mature TPRM posture are increasingly preferred by enterprise buyers, regulated industries, and partners conducting their own vendor due diligence. Your risk controls become a differentiator in procurement decisions.
-
业务复原力
When macro events disrupt supply chains, such as geopolitical crises, natural disasters, and regional conflicts, organizations with active TPRM programs are better positioned to identify exposure quickly, activate contingency plans, and maintain service continuity for their customers.
-
成本效益
A properly structured TPRM program reduces the cost of late-stage risk discovery, regulatory penalties, and incident response. Front-loading due diligence is substantially less expensive than remediating a breach, a failed audit, or a vendor-caused disruption after the fact.
-
Informed Vendor Decisions
TPRM provides the data foundation for better business decisions about which vendors to engage, at what risk tolerance, and under what contractual terms. Risk-informed vendor selection reduces exposure across every third-party relationship your organization manages.
Your TPRM Program Doesn't Have to Start from Scratch
Get the 10-step guide to building and maturing your third-party risk management program.
Download the Framework实施您的 TPRM 计划
一旦您决定实施 TPRM 计划,您将面临一系列重要问题,这些问题将构成您计划的基础。这些问题包括
- 您是否聘请合作伙伴帮助您启动和实施计划?
- 如何管理内部利益相关者的期望?
- 发生数据泄露时,您需要分配责任吗?
- 第三方开展业务必须满足哪些确切要求?
- 外部利益相关者是否理解需求并能够执行需求?
- 实施这些要求是否会改变与供应商的财务关系?
- 如何在现有关系中推广该计划?
Organizations must focus on bringing together the right people, processes, and technologies to implement a 3rd party risk management program. Understanding the balance and the requirements of each of these functions is critical to the successful operation of your program.
为应对 TPRM 环境中的风险,您应在以下方面启用组织标准和语言:

- 制定合同和服务水平协议要求,以履行与风险相关的承诺。
- 根据业务约定或所提供服务的风险状况分析供应商的风险状况。
- 通过动态监控和基于事件的风险评估,实现报告流程。
- Mix periodic risk assessments (self-reported) and continuous risk monitoring (externally reported) approaches for end-to-end risk identification.
- 实施技术解决方案,将采购、绩效和风险管理整合到一个统一的平台上,为利益相关者提供最新信息,满足他们的特定需求。
It is important to note that in building relationships with internal and external stakeholders, not all incentives have to be punitive or restrictive. Establishing contract or service level agreement requirements should include minimum performance standards but can also include “rewards” for compliance with critical risk management functions. Additionally, analyzing the vendor’s requirements versus your organization’s can provide enormous dividends for both parties. By leveraging existing compliance, it is possible to reduce the costs for both parties to their mutual benefit.
Effective TPRM implementation requires the right technology and the organizational infrastructure to support it: documented workflows, defined risk tolerances, stakeholder alignment on escalation triggers, and a plan for onboarding vendor relationships already in flight. Organizations that mature quickly typically start with a narrow, well-governed scope and expand it. Still, whether you’re building incrementally or standing up a full program, the right partner can accelerate both the design and the execution.
See How Mitratech TPRM Can Help you Scale and Streamline Vendor Risk Management
Get Started Here常见问题
What is inherent risk scoring in TPRM?
Inherent risk scoring measures the risk a vendor poses based on their internal controls and business practices, before your organization’s specific requirements are applied. It determines the appropriate level of due diligence and sets the frequency and scope of subsequent assessments. A vendor with access to sensitive customer data and no formalized security program will carry a higher inherent risk score than one with third-party audit certification.
What is the difference between periodic risk assessments and continuous risk monitoring?
Periodic assessments are structured, questionnaire-based evaluations conducted at defined intervals, such as during onboarding, annually, or at contract renewal. Continuous monitoring draws on external intelligence sources in near real time to surface cyber, financial, and reputational risks between intervals. Together, they provide a more complete picture of vendor risk than either approach delivers alone.
What role do regulations play in TPRM?
Regulatory frameworks across industries, including HIPAA for healthcare, PCI DSS for payment processing, GDPR for data privacy, and CMMC for federal contracting, mandate specific third-party risk controls that organizations must extend to their vendors. In many cases, the primary organization is held accountable for vendor non-compliance, not just its own. A structured TPRM program provides the documentation and audit trails regulators expect.
What tools are used for third-party risk management?
TPRM programs typically rely on questionnaire and assessment management platforms, continuous monitoring solutions, vendor intelligence networks, and workflow automation tools that route assessments and track remediation. Organizations running manual processes consistently report slower risk identification and higher rates of assessment errors. Compare leading platforms or review the top TPRM approaches if you are still evaluating which model fits your program.
Editor’s Note: This post was originally published on Prevalent.net. In October 2024, Mitratech acquired the AI-enabled third-party risk management platform, Prevalent. The content has since been updated to include information aligned with our product offerings, regulatory changes, and compliance.



