Whistleblower protection expectations continue to expand across regions, industries, and regulator priorities. In 2026, organizations will be held to higher standards for speed, security, transparency, and auditability than ever before.
Between the EU Whistleblower Directive and evolving U.S., U.K., and APAC requirements, compliance leaders must manage complex, multi-jurisdictional obligations while protecting anonymity where required, preventing retaliation, and maintaining employee trust.
If you haven’t reassessed your existing ethics hotline program within the last 12 months, it likely needs updating. To address all the new requirements and trends, we outlined the essential steps to building a modern, global whistleblower protection program; one that centralizes intake and case management, aligns legal obligations by region, secures reporting channels, and delivers defensible, audit-ready investigations.
Whether you’re updating an existing hotline or designing a program from the ground up, these best practices will help legal, HR, and compliance teams reduce risk, meet regulatory expectations, and strengthen a resilient speak-up culture.
1. Centralize Whistleblower and Ethics Hotline Management
Establish a single, unified system to manage whistleblower and ethics hotline activity across legal, HR, and compliance teams. Centralization streamlines secure intake, automated routing, consistent case documentation, and complete audit trails. It also reduces fragmentation and manual handoffs.
Best-in-class programs use workflow automation to enforce mandated timelines, apply role-based access, and ensure consistent triage across all reports. Built-in risk detection helps teams identify and prioritize high-severity matters early, while configurable rules support multi-jurisdictional whistleblower requirements without duplicating tools or processes.
To further strengthen oversight, integrate hotline operations with external reporting channels, HRIS and ITSM platforms, data loss prevention and forensics tools, and analytics systems. The result is faster, more defensible investigations, improved regulatory readiness, and fewer organizational silos—while maintaining employee trust and confidentiality.
Note: For organizations operating within the EU, implement dedicated subsidiary reporting channels to meet European Commission expectations. Any centralized data must exclude identifiable information and details without explicit consent.
2. Map Legal Obligations by Jurisdiction
Start by mapping whistleblower protection laws by country to determine how they cover protected disclosures, retaliation standards, deadlines for acknowledgments/updates, record retention, and anonymity rules. Build a global framework that establishes common principles such as confidentiality, anti‑retaliation, and timelines, and supplement it with local playbooks that reflect national specifics and language practices. This reduces cross-border conflicts, supports local works councils or unions, and simplifies interactions with regulators.
Document who is covered between employees, contractors, and suppliers, what is protected (fraud, privacy, ESG, AI risks), and how evidence must be handled. Note compliance with national transpositions, authorities’ guidance, and relevant non-whistleblowing specific regulations, such as data protection laws.
| Region | Core obligation | Key timelines | Reporting requirements | Retention |
| EU (Directive) | Internal channels for 50+ employees | Acknowledge ~7 days; follow‑up ~3 months | Written, in person and/or oral (including voicemail) Note: Very few Member States require all reporting options (i.e., Sweden) |
Typically 2–5 years |
| U.S. (SEC/DOJ) | No retaliation; reward programs | Prompt, reasonable updates | Multiple channels; secure, anonymous | As per agency guidance |
| U.K. | Protected disclosures to prescribed persons | Timely feedback recommended | Confidential channels; fairness duty | Per ICO/data rules |
| Canada | Anti‑reprisal; sectoral rules | Reasonable timelines | Multilingual advisable | Statute‑dependent |
| APAC | Varies (Japan, Australia strong) | Statute‑specific | Localized access and privacy | Local law‑driven |
Key Takeaway: Mapping legal obligations globally creates a harmonized framework while accommodating local nuances.
Is your whistleblowing program audit-ready?
Download the White Paper: Global Whistleblowing Regulations & GRC: A Strategic Imperative for Modern Governance
Get the Insights3. Provide Secure, Accessible Reporting Channels
Offer multiple reporting channels to meet employees where they are. This includes web portals, phone options like IVR or live agents, mobile apps, in-person reporting, and postal mail. Ideally, these methods are supported by multilingual, anonymous two-way messaging for follow-up questions and evidence sharing.
The EU Whistleblower Directive allows Member States to require both written and oral reporting options, including voicemail. Your reporting system should securely record submissions, protect sensitive data, and strictly limit access to authorized roles.
Apply rigorous anonymization standards across all channels. Avoid IP logging, use end-to-end encryption, enable pseudonymous inboxes, and maintain secure, auditable workflows for ongoing communication. Make channel availability clear and consistent—24/7, across regions and devices—and communicate confidentiality and non-retaliation commitments prominently to build trust.
Key Takeaway: Offering multiple, secure, multilingual reporting channels strengthens trust and supports compliance with diverse regulatory requirements
4. Lock Down Technical Protections
Your ethics hotline and case management system must operate at enterprise-grade security standards. Protect data at rest and in transit with AES-GCM encryption and modern TLS. Deploy the platform in hardened cloud environments, enforce MFA and SSO, and apply role-based access controls using least-privilege principles.
Design for privacy from the start. Where possible, adopt zero-knowledge or privacy-by-design architectures, supported by strong key management, network segmentation, and comprehensive logging. True anonymity requires more than policy statements. It depends on technical controls, including no IP logging, end-to-end encrypted sessions, and secure, anonymous follow-up channels.
Validate vendor security continuously, not just at onboarding. Require regular penetration testing, independent certifications such as SOC 2 and ISO 27001, clear data processing agreements, and regulator-aligned data retention and deletion policies. Use a structured technical checklist during procurement and annual reviews to satisfy auditors and reinforce trust with reporters.
Key Takeaway: Strong encryption, enforced identity controls, and privacy-first architectures protect anonymity, withstand regulatory scrutiny, and build confidence with both auditors and reporters.
5. Design Auditable Case Management
Regulators expect reproducible investigations with complete documentation. Use whistleblower case management that maintains immutable audit trails, timestamps intake, screening, escalation, and closure, and stores evidence with chain-of-custody controls. Add structured case categorization and risk indicators to support consistent triage and escalation.
Align retention rules to each jurisdiction and restrict access by role and need-to-know. Make workflows transparent with clear SLAs and standardized templates for intake notes, interviews, and outcome summaries. The sample milestones below illustrate the kind of audit-friendly trace a reviewer should be able to follow without manual reconstruction.
| Phase | Auditable artifacts |
| Acknowledge | Receipt, anonymized message |
| Initial triage | Risk score, classification |
| Investigation | Interview logs, evidence chain |
| Updates | Reporter comms, status notes |
| Closure | Outcome, remediation plan |
Key Takeaway: Auditable case management with clear milestones helps support consistent investigations and regulatory expectations.
6. Standardize Triage and Risk Scoring
As report volumes rise, a standardized triage model keeps cases moving and reduces misclassification. Define severity criteria such as regulatory breach, safety, financial impact, and build a risk score that combines allegation type, potential harm, seniority implicated, and data sensitivity. Automate routing to legal, HR, or privacy based on thresholds, and maintain an exceptions path for conflicts of interest.
Use structured intake forms to capture key facts, the implicated controls, and the required preservation steps. Common pitfalls such as backlogs, bias, and inconsistent labeling are mitigated by clear playbooks, reviewer training, and weekly queue health checks with metrics on case age, status, and reassignment. If you apply automation or AI to support triage (for example, categorization or summarization), keep it transparent, human-reviewed, and aligned to your organization’s risk appetite.
Key Takeaway: Standardized triage and risk scoring prevent backlogs and bias, enabling swift, prioritized handling.
7. Integrate Cross‑Functional Workflows
Whistleblower matters often touch employment, privacy, financial controls, and regulatory obligations simultaneously. Map decision rights and escalation paths so legal handles potential regulatory exposure, HR addresses workplace conduct, and privacy manages data-transfer constraints. Define evidence custody steps, including legal holds, forensic imaging, and cross-border transfer assessments, and log those actions in the case record.
Build coordination checkpoints where functions validate findings and remediation before closure. Document everything to demonstrate fairness, proportionality, and timeliness. Automating handoffs inside your system reduces leakage, accelerates cycle time, and improves evidence quality across jurisdictions.
Key Takeaway: Cross-functional workflow integration aligns legal, HR, and privacy actions to deliver coordinated compliance evidence.
8. Maintain Transparent Feedback Loops
Timely communication reduces escalation risk and supports confidence in internal reporting. Configure acknowledgment within seven days, status updates at defined intervals (e.g., every 30 days), and closure notices that summarize outcomes and next steps when permitted. Enable secure, anonymous two-way messaging so reporters can add evidence and clarify details without revealing their identity.
Log every message to the audit trail and use templates to maintain a consistent, legally appropriate tone. Clear expectations around timing and confidentiality build trust and help keep issues internal rather than moving straight to regulators or the media.
Key Takeaway: Consistent, documented feedback loops support trust and help reduce retaliation risk.
9. Train Investigators and Frontline Staff
Refresh training annually to reflect new rules, cyber and AI risks, ESG allegations, and regional cultural norms. Train investigators on neutrality, evidence preservation, interview practices, and documentation standards, including scenario-based exercises for conflicts, regulatory reporting triggers, and cross-border transfer constraints.
Frontline managers should recognize protected disclosures, avoid retaliation, and escalate promptly. Provide microlearning on hotline etiquette, confidentiality, and data minimization. Track completions, validate knowledge, and align training with role-based access in your case system to ensure staff actions align with current expectations.
Many organizations overlook the importance of training potential whistleblowers, i.e., employees and other stakeholders who might be within the legally required or desired scope of reporters. Make training accessible by considering cultural particularities and language capacities. Training should never be one-off, but a recurring obligation.
Key Takeaway: Ongoing training helps ensure consistent, compliant handling of disclosures across regions and roles. The better stakeholders understand what whistleblowing is about, the higher quality reports you are likely to receive.
Discover Mitratech Compliance Training
Get in Touch10. Test, Audit, Measure Program Effectiveness
Test your program regularly to ensure it performs under real-world conditions. Run quarterly tabletop exercises to validate intake, triage, crisis escalation, and regulator notification workflows. Supplement internal testing with periodic third-party audits that assess security controls, process adherence, and investigation quality.
Use dashboards to monitor trends and risk hotspots by location, business unit, and allegation type. Track performance metrics that matter, i.e., time to acknowledge, time to triage, time to close, and reporter satisfaction, to identify gaps and prioritize action. Summarize results in a management scorecard and share trend insights with executive leadership and the board.
Act on what the data shows. Update policies, playbooks, and tools immediately, then re-measure to confirm improvement. Strong, consistent measurement signals a living program, one that adapts to evolving risks and regulations, strengthens culture, and demonstrates effective compliance to regulators and stakeholders.
| KPI’s to Track | Purpose |
| Acknowledge time | Regulatory and trust metric |
| Triage time | Queue health and prioritization |
| Case cycle time | Investigation efficiency |
| Update cadence | Transparency and fairness |
| Repeat reporting rate | Trust in internal channels |
Key Takeaway: Regular testing, audits, and KPI monitoring keep the program effective and demonstrably compliant.
11. Align Incentives and Culture
Build a strong speak-up culture by pairing enterprise-grade technical controls with visible executive sponsorship, impartial investigations, and clearly communicated non-retaliation commitments. Promote independent or third-party reporting channels to reduce concerns about bias, localize messaging to reflect cultural norms, and recognize teams that remediate root causes quickly while protecting confidentiality.
Track employee sentiment through surveys and message testing, then respond quickly with policy updates or targeted training. Because external whistleblower incentives may exist in certain enforcement actions, aligning internal trust and incentives is critical to encourage employees to raise concerns internally first.
Key Takeaway: Aligning incentives and culture promotes a speak‑up environment and mitigates retaliation.
12. Analyze and Improve
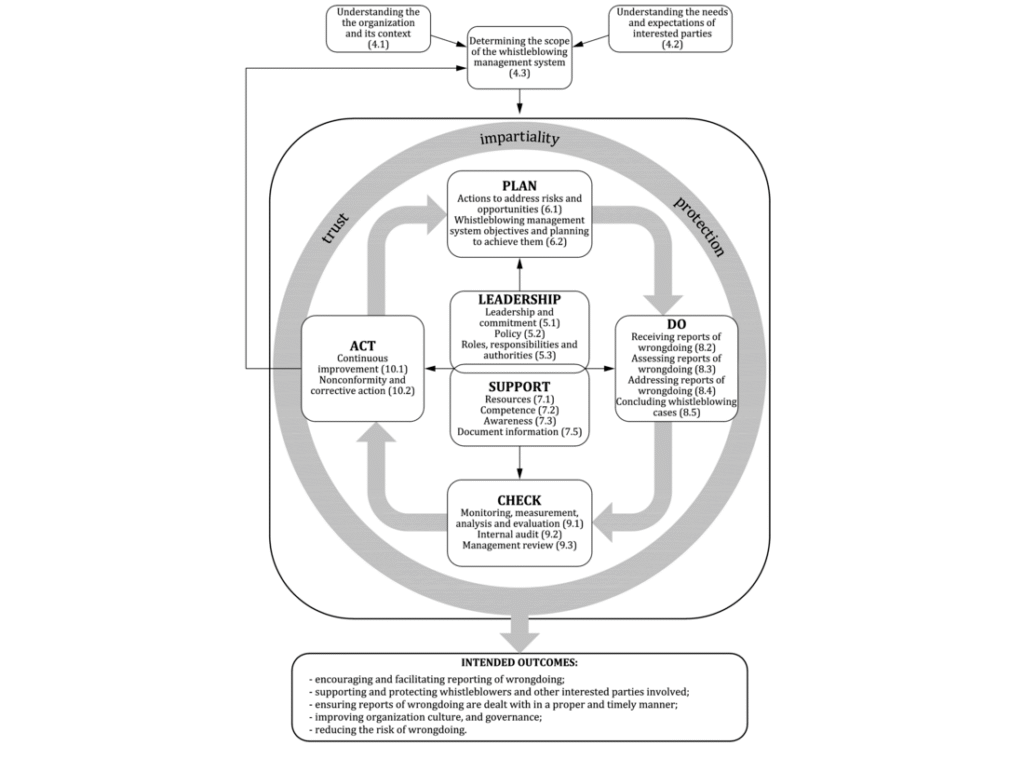
An effective whistleblower program is a continuous cycle rather than a linear process, as illustrated by the ISO 37002 figure below. Once a case is closed, organizations must reassess the entire lifecycle and identify specific opportunities for improvement. To gauge the program’s true maturity, compliance leaders should compare internal performance metrics against external industry benchmarks.
Figure 1: Whistleblowing Management Process Cycle Source:ISO Standard 37002
The data gathered from these analyses should lead to immediate action. Whether it involves updating local playbooks, refining investigator training, or adjusting risk-scoring thresholds, these improvements signal a living program. By treating every case as a data point for growth, you demonstrate to both stakeholders and regulators that your organization is committed to a resilient speak-up culture.
Key Takeaway: Continuous analysis ensures the program adapts to evolving risks, remains demonstrably compliant, and maintains long-term trust from reporters.
Conclusion
By following these essential steps — mapping global obligations, offering secure multi-channel reporting, strengthening technical safeguards, building auditable case management, standardizing triage, integrating cross-functional workflows, maintaining transparent communication, training staff, and continuously testing and measuring while reinforcing a nonretaliation culture — organizations can build a resilient whistleblower protection program for 2026.
A program that protects reporters and produces audit-ready evidence also helps reduce risk, improve responsiveness, and strengthen organizational integrity.
See how Mitratech can support your program needs. Get in touch with our team of experts today.